Keeping your computer’s operating system up to date is rudimentary to retaining the gadget cozy. Why? Whether your laptop is constructed around a Windows, Mac, Unix, or Linux-primarily based running gadget (OS), the builders of the running machine – whether maintained commercially or through open supply groups – try to enhance the abilities, features, and most significantly, the security of the system. When a producer releases a new OS, they’re now not just trying to make the most of a new product; they’re striving to produce and distribute a better product. In fact, the trendy trend beyond the year in industrial operating structures released by using top companies in the industry (i.E., Apple, and Microsoft) is to offer purchasers FREE improvements to the state-of-the-art working device. This means that businesses are not even benefiting from the distribution of their modern-day device. So why not improve your computers’ working systems whilst there are not any financial expenses concerned?
Going lower back to why builders change operating systems on an ordinary and ongoing basis, at the same time as it has the whole thing to do with commercial enterprise, best a fragment is ready income. One of the greatest benefits of a free marketplace is that organizations will compete to produce a better, extra acceptable product. While competing to enhance products, in this case, running structures, the builders strive to decorate truly all aspects of a device, along with however virtually now not confined to its safety functions. However, this is not an editorial on economics on why customers have to a consciousness of the benefits of upgrading computers’ working systems, as opposed to the drawbacks, and how upgrading the OS may also improve the safety of the laptop and the person’s facts its stores.
Often customers have kept computers on the identical working device (generally the OS pre-established when the computer becomes bought) for years or even a long time. Non-technical users will hesitate to improve the OS to avoid making any adjustments that would smash the pc, or worse – would possibly rearrange the computer, menus, and toolbars in this type of manner that it is tough for the user to navigate or utilize. We get it; the exchange is scary. When computer systems and menus change appearance and options are relocated, it may be tough to alter to the brand new format. Yet, if a person can conquer the brief inconveniences of navigating a new running machine, he or she can enjoy the comforts and assurances that come with the improvement.
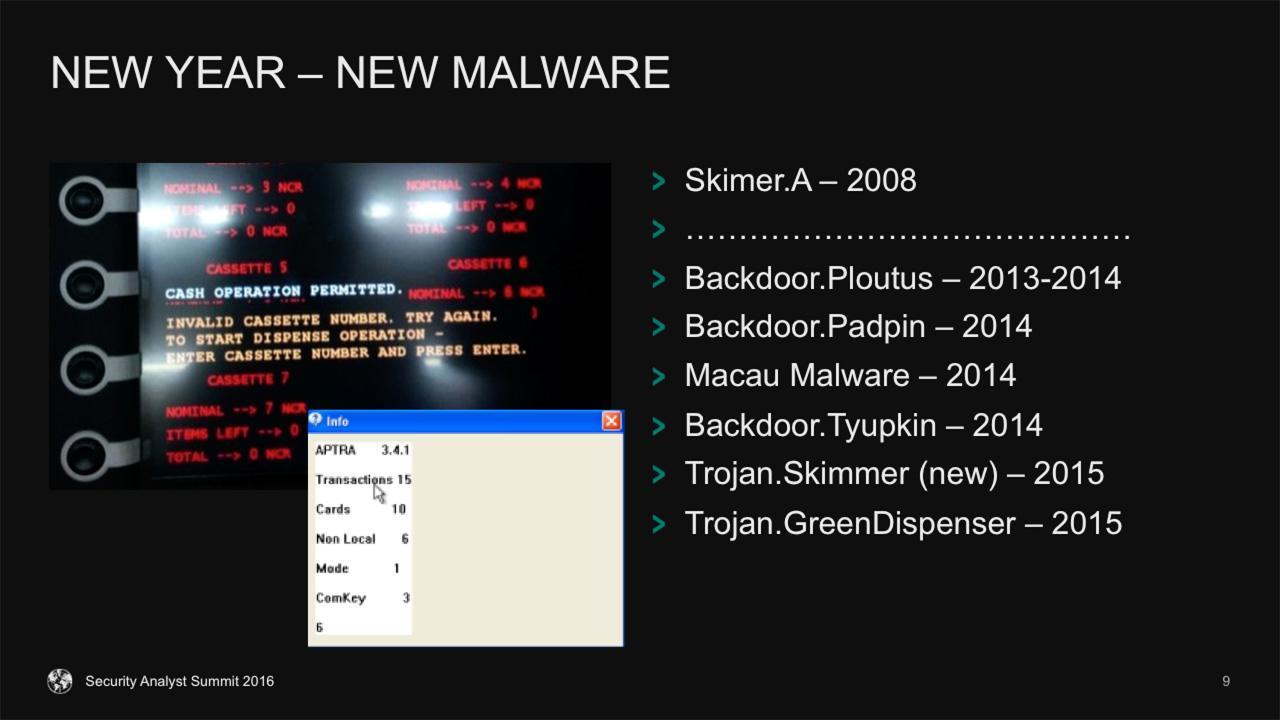
Over a period of time, the number of exploits into any (and each) type of OS will increase the way to penetration testers, hackers, and malware builders. The truth of the matter is that the longer a machine is in motion, the longer programmers had been attempting to exploit it through hacks, cracks, malware, and different hints. It is an in no way-finishing sport of breaching and patching a gadget that makes it greater comfy. The problem with legacy working structures is that the word legacy is meant to describe a product that is no longer supported via the manufacturer – is that any newly observed vulnerabilities in the gadget will never be patched or secured. Security vulnerabilities can allow attackers and/or malware to bypass network protocols, execute far-flung codes, improve get entry to privileges to device packages and files, expose or acquire user profile statistics, corrupt gadget drivers or documents, purpose a denial of provider, and carry out other activities that might damage the user, the device, and/or utility(s).






